Current News
/ArcaMax
Columbia University extends deadline for students to clear pro-Gaza encampment
NEW YORK — Columbia University extended a deadline overnight for student protesters to clear their campus antiwar tent encampment, giving them another 48 hours to pull up stakes and leave, school officials said Wednesday.
The agreement comes just under a week after university officials called the NYPD to break up a prior iteration of the ...Read more
Blinken lands in China for tense talks as US sanctions loom
Secretary of State Antony Blinken has arrived in China on a mission to press Beijing on issues including its support for Russia and industrial overcapacity, with the threat of new U.S. sanctions looming over the visit.
The top U.S. diplomat will hold talks with senior Communist Party officials in the economic hub of Shanghai on Thursday, ...Read more
Decades of dallying led to current delay on menthol ban
The Biden administration’s delay in finalizing a ban on menthol cigarettes is the result of decades of resistance, delays and industry lobbying, according to former officials and public health advocates.
The White House blew past a self-imposed deadline to finalize the proposal in March after missing a previous deadline in August. Advocates ...Read more
North Korea stokes arms concerns by sending a rare delegation to Iran
North Korea sent its highest-level delegation to Iran in about five years as the U.S. raised concerns that arms sales from Pyongyang and Tehran have helped fuel conflicts in the Middle East and Russia’s war in Ukraine.
In a rare public report of the trip, the official Korean Central News Agency said in a one-sentence dispatch the North Korean...Read more
States move to label deepfake political ads
WASHINGTON — After 20,000 or more New Hampshire voters received a call with the artificial-intelligence-doctored voice of President Joe Biden asking them to skip the state’s primary in January, state officials were in a quandary.
Attorney General John M. Formella launched an investigation alongside others into the robocall that urged ...Read more
LA sees a surge of billboards for personal injury lawyers. You'll never guess why
LOS ANGELES — Among the myriad side effects of the pandemic: a surge in billboards and bus ads for personal injury law firms.
They seem to have sprouted all over Los Angeles.
Morgan & Morgan's blue-and-yellow billboards proudly declare "Size Matters," Jacob Emrani's ads with red cursive writing direct readers to CallJacob.com, and Pirnia ...Read more

Senate approves nearly $61B of Ukraine foreign aid − here’s why it helps the US to keep funding Ukraine
The Senate overwhelmingly approved a US$95.3 billion foreign aid funding package for Ukraine, Israel and Taiwan on April 23, 2024, following months of political infighting that stalled the bill in the House of Representatives. About $61 billion of this aid package will be spent on Ukraine, while $26 billion will go to Israel. Another $8 ...Read more

Do implicit bias trainings on race improve health care? Not yet – but incorporating the latest science can help hospitals treat all patients equitably
There is increasing evidence that implicit bias – non-conscious attitudes toward specific groups – is a source of racial inequities in certain aspects of health care, and lawmakers are taking note.
Since the tragic murder of George Floyd in May 2020, wherein a Black man was killed by police, several U.S. federal and state ...Read more

Nearsightedness is at epidemic levels – and the problem begins in childhood
Myopia, or the need for corrected vision to focus or see objects at a distance, has become a lot more common in recent decades. Some even consider myopia, also known as nearsightedness, an epidemic.
Optometry researchers estimate that about half of the global population will need corrective lenses to offset myopia by 2050 if current ...Read more

Gender-nonconforming ancient Romans found refuge in community dedicated to goddess Cybele
A Vatican declaration, the “Infinite Dignity,” has brought renewed attention to how religions define and interpret gender and gender roles.
Approved by the pope on March 25, 2024, the Vatican declaration asserts the Vatican’s opposition to gender-affirming surgery and surrogacy. While noting that people should not be “...Read more

How trains linked rival port cities along the US East Coast into a cultural and economic megalopolis
The Northeast corridor is America’s busiest rail line. Each day, its trains deliver 800,000 passengers to Boston, New York, Philadelphia, Washington and points in between.
The Northeast corridor is also a name for the place those trains serve: the coastal plain stretching from Virginia to Massachusetts, where over 17% of the country...Read more
US Supreme Court hears arguments on Idaho abortion law this week. How did we get here?
The U.S. Supreme Court on Wednesday will hear arguments from the state and the U.S. Department of Justice that will determine their decision on the fate of emergency abortion access in Idaho.
Since Idaho’s strict abortion laws went into effect following the court’s repeal of Roe v. Wade in June 2022, they have faced numerous legal ...Read more

Illinois residents encouraged to destroy the eggs of invasive insects to slow spread
CHICAGO — While Chicagoans were alarmed to learn the spotted lanternfly had been found in Illinois last year, experts say spring is the time to take action against that insect — as well as another damaging invasive species that has made far more inroads and gotten less attention.
The spongy moth, formerly known as the gypsy moth, has been ...Read more

Steelhead trout, once thriving in Southern California, are declared endangered
Southern California’s rivers and creeks once teemed with large, silvery fish that arrived from the ocean and swam upstream to spawn. But today, these fish are seldom seen.
Southern California steelhead trout have been pushed to the brink of extinction as their river habitats have been altered by development and fragmented by barriers and dams...Read more

Commentary: Christian nationalism is a grave threat to America
My father, who served as a Navy officer in the South Pacific, shared fascinating World War II stories with me. With ensuing history classes, I became troubled by America’s slow response to Hitler’s atrocities in Europe and incredulous that Christians in Germany blindly followed their deranged dictator.
While pursuing a master of divinity ...Read more

Climate change supercharged a heat dome, intensifying 2021 fire season, study finds
As a massive heat dome lingered over the Pacific Northwest three years ago, swaths of North America simmered— and then burned. Wildfires charred more than 18.5 million acres across the continent, with the most land burned in Canada and California.
A new study has revealed the extent to which human-caused climate change intensified the ...Read more

Shelter dollars in Mass. 'close to running out' as funding bill sits on Beacon Hill, Gov. Healey says
BOSTON — A panel of lawmakers tasked with delivering a compromise on a spending bill that includes hundreds of millions for the state-funded shelter system appears no closer to a deal as the cash left to pay for services dwindles.
Two top Beacon Hill budget writers are privately hashing out the differences between legislation that taps ...Read more
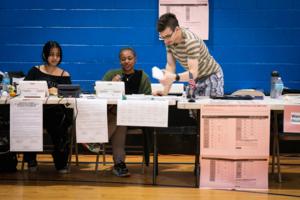
On a perfect day for voting, the Pennsylvania primary generates a 'super-low turnout'
PHILADELPHIA — A primary election day that was wall-to-wall splendid around here with unimpeded sun and a generous ration of April warmth was absolutely perfect for voting. And evidently for not voting.
With nominees already essentially chosen for president — and not everyone is happy with them — and U.S. Senate and a general absence of ...Read more

Aid finally set to flow as Senate clears $95.3 billion emergency bill
WASHINGTON — The Senate cleared a war funding package Tuesday night for President Joe Biden’s certain signature, capping a six-month struggle over Ukraine aid that divided GOP lawmakers, delayed Western weapons deliveries and gave Russia some breathing room in a military offensive against its neighbor.
The 79-18 vote to aid Ukraine, Israel ...Read more

Tensions grow at California universities as Gaza protests roil campuses from Berkeley to New York
LOS ANGELES — Officials shut down the campus of Cal Poly Humboldt on Monday night after masked pro-Palestinian protesters occupied an administrative building and barricaded the entrance as Gaza-related demonstrations roiled campuses across the nation.
Three students were arrested after law enforcement officers wearing helmets and riot shields...Read more
Popular Stories
- Senate approves nearly $61B of Ukraine foreign aid − here’s why it helps the US to keep funding Ukraine
- Illinois residents encouraged to destroy the eggs of invasive insects to slow spread
- Ex-Ecuador official found guilty of laundering millions in Odebrecht bribes in Miami
- Steelhead trout, once thriving in Southern California, are declared endangered
- Tensions grow at California universities as Gaza protests roil campuses from Berkeley to New York